

Another angle on dangers of USB-Sticks
While these days almost everybody knows the dangers of plugging-in unknown usb-sticks, this article shows the dangers of passing own usb-devices.
Raphael Kuhn
CVE Virtuoso
Datum
27/10/2024


Advisory: Avid Nexis Agent Multiple Vulnerabilites
During a customer security audit, Raphael Kuhn found some quite easy to spot bugs in the avid nexis agent
Raphael Kuhn
CVE Virtuoso
Datum
23/10/2024


Simple yet effective. Simple bugs, big impact!
By spying on the process creation of a UCS connected server with extensive permissions, it was possible to compromise an entire domain.
Raphael Kuhn
CVE Virtuoso
Datum
14/05/2024


LiveConfig Advisory (CVE-2024-22851)
During a security audit for a LiveConfig customer, Raphael Kuhn discovered a Unauthenticated Path Traversal vulnerability in LiveConfig up to version 2.5.1.
Raphael Kuhn
CVE Virtuoso
Datum
24/04/2024
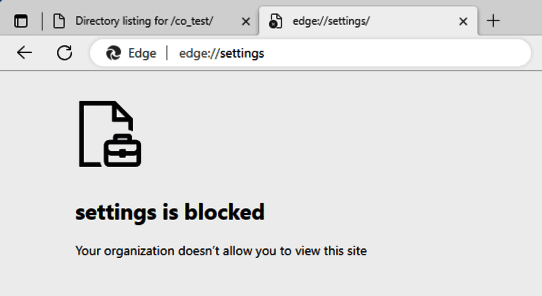
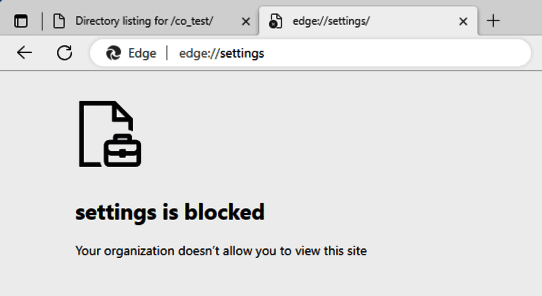
Inteset Secure Lockdown - Vulnerabilities and Hardening
During a security audit, Raphael Kuhn discovered several vulnerabilities within inteset Secure Lockdown. In this article he discloses all findings..
Raphael Kuhn
CVE Virtuoso
Datum
16/04/2024


Ransomware: Definition, FAQs and Prevention
Ransomware, from the English "ransom software", is classified as aggressive malware that encrypts hard drives of PCs until a ransom is paid.
Amir Hosh
The Professor
Datum
04/10/2021


Phishing: What it is and how you can prevent it
Phishing represents a criminal conduct and targets unsuspecting employees and urges them to share sensitive and information.
Amir Hosh
The Professor
Datum
19/09/2021